ANATOMI OF A PANIC: DECONSTRUCTING THE “QUANTUM APOCALYPSE” FALLACY
Mass hysteria is often a byproduct of technical illiteracy. In the digital asset cycle, the “Quantum Apocalypse” narrative is a perennial ghost story; it resurfaces every time Google or IBM announces a laboratory breakthrough.
The narrative is simple, viral, and lethal to weak hands: “Quantum computers will process data so fast they will derive your Private Key in seconds, sending $1.4 trillion in market cap to zero.”
This thesis is fundamentally flawed. To understand the true risk profile—and why institutional giants like BlackRock and Fidelity maintain their exposure—we must dismantle this myth at the level of particle physics. The issue is not speed; the issue is probability.
BEYOND BINARY: THE PHYSICS OF PROBABILITY
The primary error among retail observers is viewing a quantum computer as a “Turbo” version of a classical machine. They imagine a classical computer is a race car, while a quantum computer is a rocket. This analogy is dangerously misleading.
Classical computers (binary) operate deterministically. They process information in bits: 0 or 1. Picture a mouse navigating a maze; it tries one path, hits a wall, returns, and tries another. It operates linearly and sequentially.
Quantum computers operate on different physics. Utilizing a principle of quantum mechanics known as Superposisi, the processing unit (Qubit) exists as 0, 1, or both simultaneously. Returning to the maze analogy: a quantum computer does not send a single mouse. It floods the entire maze with water instantly. The water locates the exit immediately because it occupies all possible paths at the same time.
In cryptography, this means a quantum machine does not “guess passwords rapidly” (classic brute force). Instead, it utilizes specific algorithms to collapse the mathematical structure protecting the key. However, this weapon is not universal. We must distinguish between two mathematical vectors: Shor’s Algorithm and Grover’s Algorithm.
THE SNIPER: SHOR’S ALGORITHM AND THE ASYMMETRIC VULNERABILITY
This is the genuine existential threat, though its timeline is widely misunderstood.
Bitcoin’s security—and the security of the global banking layer—relies on Asymmetric Cryptography, specifically Elliptic Curve Cryptography (ECC) on the secp256k1 curve. The premise relies on a “Trapdoor Function”: it is computationally trivial to multiply two large prime numbers to generate a Public Key, but thermodynamically impossible for a classical computer to reverse that operation to derive the Private Key.
Shor’s Algorithm, when executed on a sufficiently powerful quantum machine, solves this Discrete Logarithm Problem efficiently.
If Shor’s Algorithm functions perfectly with adequate Qubit capacity, it reduces the complexity of breaking the key from exponential to polynomial. Effectively, the mathematical firewall protecting Bitcoin signatures could be breached. This is a “Sniper” targeting the transaction signature mechanism. Yet, as we will explore, Bitcoin possesses a defensive layer that banking SSL certificates lack: Hashing.
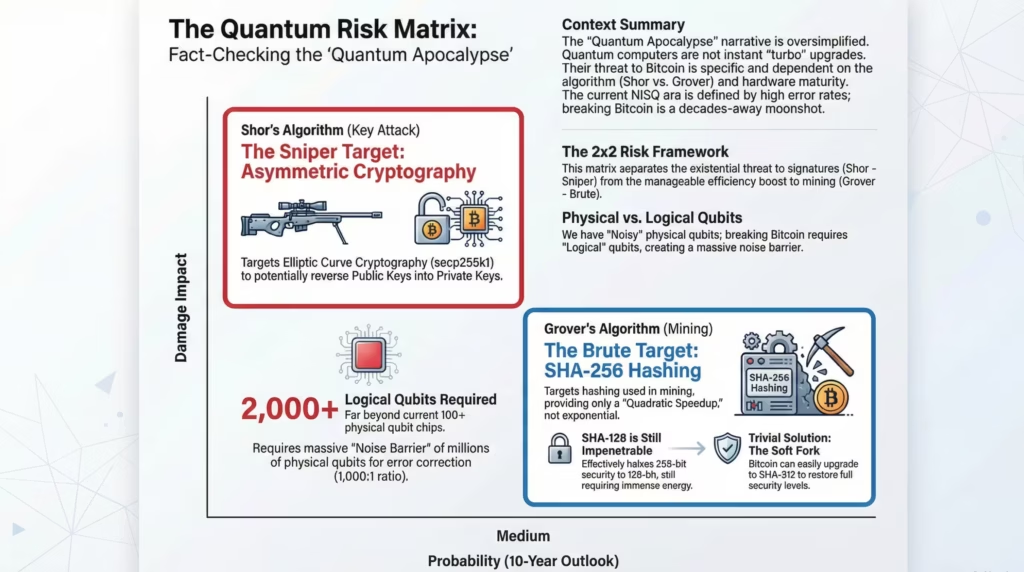
THE BRUTE: WHY GROVER’S ALGORITHM FAILS AGAINST SHA-256
Mainstream media frequently conflates quantum algorithms. Grover’s Algorithm operates on entirely different mechanics and poses a negligible threat to the Bitcoin network.
Grover is designed for unstructured database searches. In the context of digital assets, it attacks the SHA-256 (Secure Hash Algorithm) function used for mining and address generation.
The reality: Grover’s Algorithm only provides a “Quadratic Speedup,” not the exponential jump seen in Shor’s. Translated to encryption security standards: Grover effectively halves the security bits of symmetric encryption.
- SHA-256 (256-bit security) faces a quantum threat equivalent to SHA-128 (128-bit security).
Is SHA-128 insecure? Practically, SHA-128 remains impenetrable. Cracking it via brute force would require energy output exceeding that of our sun. Consequently, the narrative that “Bitcoin Mining is dead” or “Hashing is broken” is mathematical fiction. Furthermore, if the threat from Grover accelerates, the remediation is trivial: Bitcoin executes a Soft Fork to upgrade to SHA-512, instantly restoring full security margins.
THE NOISE BARRIER: THE “WILLOW” CHIP AND THE REALITY OF LOGICAL QUBITS
Why has the network remained secure despite Google announcing the “Willow” quantum chip with 105 Qubits?
There is a massive divergence between Physical Qubits (produced by Google/IBM) and Logical Qubits (required to run Shor’s Algorithm).
Physical Qubits are notoriously volatile. They suffer from decoherence—loosing their quantum state due to microscopic heat or cosmic radiation. To execute complex calculations like deriving a Private Key, we require Logical Qubits that are stable and possess error-correction capabilities.
Current consensus among physicists is stark: To create 1 Logical Qubit, we require between 1,000 and 10,000 Physical Qubits working in unison strictly to correct errors.
To break Bitcoin’s secp256k1 encryption, rough estimates suggest we need 2,000 to 4,000 Logical Qubits. Multiplied by the error correction ratio, the hardware requirement swells to millions of Physical Qubits.
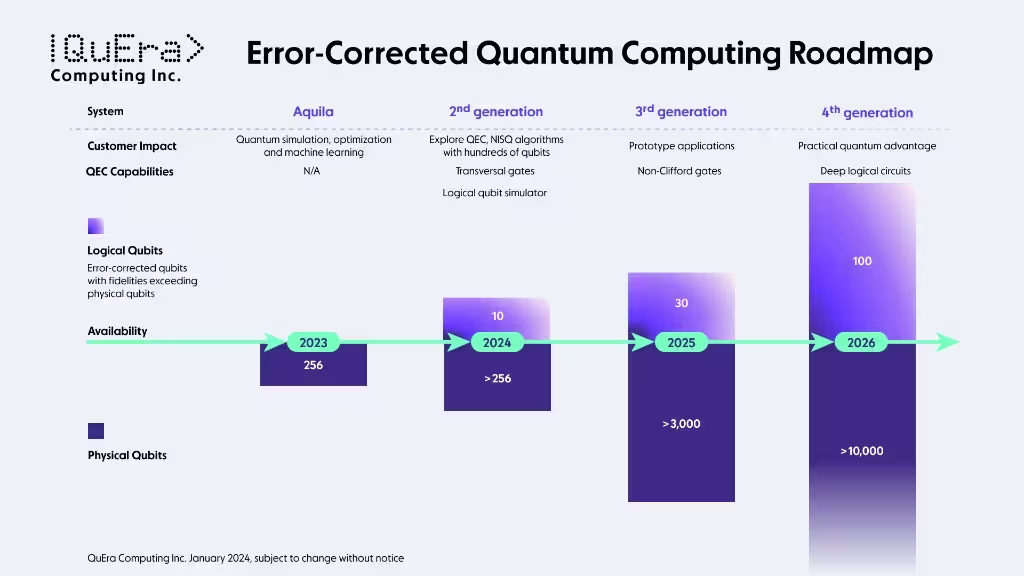
Today, we are in the hundreds, operating with high error rates (the NISQ Era – Noisy Intermediate-Scale Quantum). Scaling from 100 to 1,000,000 is not a software update; it is an engineering challenge comparable to the moon landing. The gap between “theoretically possible” and “industrially capable” is separated by decades of innovation in materials science and cryogenics. “Q-Day” is not an event for tomorrow morning; it is a slowly moving horizon.
THE ARCHITECTURE OF IMMUNITY: BITCOIN’S DOUBLE-VAULT STRUCTURE
If one assumes Bitcoin’s security relies on a single layer of “unbreakable” encryption, they have failed their technical due diligence. The most common error in retail analysis is the assumption that a Bitcoin Address is identical to a Public Key. This represents a fundamental misunderstanding of the protocol’s defense-in-depth architecture.
To understand why even a functional quantum computer would hit a mathematical wall when attempting to seize assets, we must dissect the two pillars of the protocol: The Elliptic Curve (ECDSA) and the Hashing Shield.
THE GLASS DOOR: ECDSA AND THE STRUCTURAL VULNERABILITY
We must first address the legitimate vulnerability; the vector most cited by bear cases. The heart of Bitcoin’s digital signature scheme is the ECDSA (Elliptic Curve Digital Signature Algorithm), specifically utilizing the secp256k1 curve.
The mechanism operates as a classic trapdoor function:
- You generate a Private Key (a massive random integer).
- Through elliptic curve point multiplication, this derives a Public Key.
- The mathematical relationship is asymmetric: computing Public from Private is trivial, but reversing Public to Private is classically impossible.
This is where Shor’s Algorithm becomes relevant. If an attacker possesses your Public Key, a quantum computer with sufficient Logical Qubits (in the thousands) could theoretically reverse this operation. The algebraic structure of elliptic curves is susceptible to quantum superposition attacks.
If the protocol ended here, the asset class would face a critical risk. Every time a user shared a wallet address, they would essentially be handing the blueprint of their vault to the adversary. However, the architecture does not end here.
THE INVISIBLE SHIELD: WHY HASHING IS NOT ENCRYPTION
This is the “Alpha” that mainstream media overlooks: Your Bitcoin Address is NOT your Public Key.
A standard Bitcoin address (starting with ‘1’, ‘3’, or ‘bc1’) is the result of a rigorous Double-Hashing process applied to the Public Key. The sequence is precise:
- The Public Key is generated.
- It is hashed using SHA-256.
- The result is hashed again using RIPEMD160.
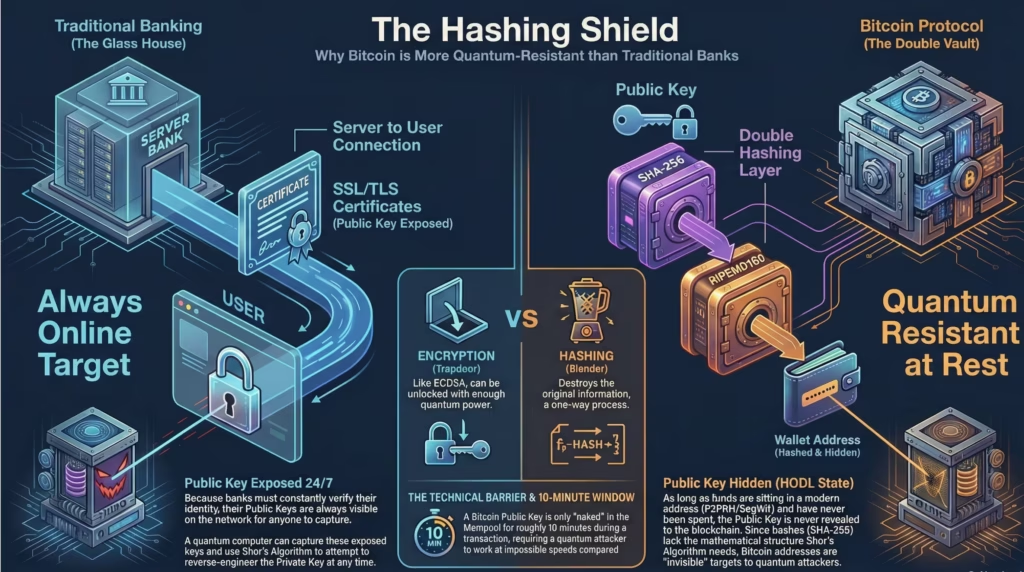
The distinction between Encryption (ECDSA) and Hashing (SHA-256/RIPEMD160) is fundamental to the thesis. Encryption is designed to be decrypted with a key. Hashing is designed to destroy information. Hashing is akin to shredding a classified document into microscopic pulp; you cannot reconstruct the original document from the pulp, regardless of your computational speed.
The Strategic Implication:
Shor’s Algorithm CANNOT attack a Hash function. It requires a specific mathematical structure (like elliptic curves or prime factorization) to exploit. Hashing functions are pseudo-random and lack this structure.
Consequently, as long as an address has never sent a transaction (it has only received or HODLed), the Public Key has never been exposed to the internet. It remains concealed behind the SHA-256 firewall. A quantum computer has no target to lock onto. To a quantum attacker, a modern Bitcoin wallet (P2PKH) is an invisible black box.
THE ECONOMIC MOAT: WHY QUANTUM MINING IS A LOSING TRADE
Beyond theft, the secondary fear is network capture: “Could a quantum entity mine the remaining Bitcoin instantly and execute a 51% Attack?”
The probability is near zero, and the reason is purely economic.
Bitcoin mining relies on the SHA-256 function. As established, the relevant quantum attack vector here is Grover’s Algorithm, not Shor’s. Grover offers only a “Quadratic Speedup,” which is insufficient to break the game theory of mining.
Consider the simulation:
- If an attacker deploys quantum hardware for mining, they will achieve higher efficiency than general classical computers.
- However, Bitcoin utilizes an automated Difficulty Adjustment every 2,016 blocks (approximately two weeks).
- If the hashrate surges due to quantum entrants, the network automatically recalibrates the difficulty to an astronomical level.
The result is a diminishing return. Furthermore, current ASIC (Application-Specific Integrated Circuit) miners are millions of times more efficient at the specific task of SHA-256 hashing than general-purpose machines. A quantum computer—likely costing billions and plagued by error rates—would likely possess a worse cost-per-hash ratio than a modern ASIC farm. Deploying a $10 billion quantum machine to mine Bitcoin is capital allocation malpractice; it is akin to using a Space Shuttle to deliver a pizza.
FORENSIC RISK ASSESSMENT: QUANTIFYING THE “NAKED” EXPOSURE
Data is the antidote to hysteria. While the narrative suggests a systemic collapse, the on-chain reality is far more contained. Recent institutional intelligence from CoinShares (led by Christopher Bendiksen) reveals a statistic that effectively neutralizes the panic: Of the 19.7 million Bitcoin in circulation, only approximately 10,230 BTC are technically “exposed” and vulnerable to a contemporary quantum attack.
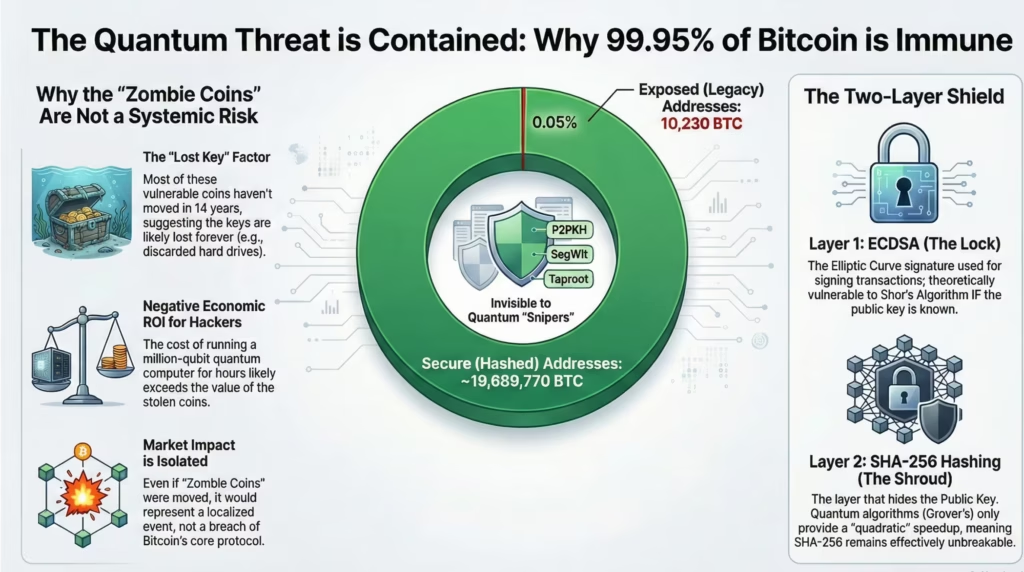
Why is the risk exposure so minimal (<0.06% of supply)? To understand why the vast majority of the network is armored while this small cohort remains “naked,” we must analyze the Darwinian evolution of the protocol’s architecture: the shift from P2PK to P2PKH.
PROTOCOL EVOLUTION: FROM GLASS HOUSES TO STEEL VAULTS
To understand the attack surface, we must revisit the legacy infrastructure of the Satoshi era (2009-2010).
1. The Legacy Vector: P2PK (Pay-to-Public-Key)
In the Genesis era, the protocol utilized a rudimentary transaction script known as P2PK.
- The Mechanism: Funds were locked directly to the Public Key (a point on the elliptic curve). The Public Key was explicitly visible in the transaction output (UTXO).
- The Vulnerability: Because the Public Key is exposed on the ledger in perpetuity, these addresses are the only valid targets for Shor’s Algorithm. They lack the hashing layer entirely. We classify these as “Glass Wallets.”
2. The Modern Standard: P2PKH (Pay-to-Public-Key-Hash)
Recognizing the efficiency and security implications, the network migrated to P2PKH.
- The Mechanism: Funds are locked to the Hash of the Public Key.
- The Defense: As detailed in the previous section, the Public Key remains obfuscated by SHA-256 and RIPEMD160 until the moment of spending. These are “Steel Vaults.”
The absolute majority of the current supply—including custody held by BlackRock, MicroStrategy, and modern retail wallets—resides in P2PKH (or superior SegWit/Bech32 standards). They are effectively invisible to quantum radar.
THE ZOMBIE THESIS: PROFILING THE 10,000 BTC COHORT
The 10,230 BTC identified by CoinShares is not a random sample. It is a specific, dormant cohort identified through rigorous on-chain forensics. These are UTXOs using the legacy P2PK script that have not moved since their creation.
The profile of these assets suggests they are not active risks, but rather “Zombie Coins”:
- Vintage: Almost exclusively mined in 2009-2010, when the asset had zero market value and was circulated among cypherpunks via email.
- Distribution: The supply is fragmented across thousands of wallets with negligible balances (<50 BTC).
- Status: These assets remained dormant when price discovered $1, $1,000, and $73,000. In forensic accounting, this is the strongest indicator of Lost Keys. These are effectively stranded assets.
THE ECONOMIC PARADOX: WHY HACKERS WON’T TARGET THE VULNERABLE
This presents the ultimate irony of the quantum narrative: The only technically vulnerable targets (P2PK) are the most economically irrelevant.
If a hostile state actor successfully engineers a quantum computer with millions of Logical Qubits, targeting this 10,000 BTC cohort faces a fatal ROI (Return on Investment) paradox:
1. The Cost of Attack:
Operating a quantum supercomputer involves operational expenditures (OpEx) in the millions per hour. Targeting thousands of fragmented, small-balance addresses is economically inefficient. A rational attacker requires a “Whale” wallet to justify the compute cost.
2. The Migration of Whales:
Active institutional capital (“Smart Money”) has long migrated to modern P2PKH or Multi-Sig Cold Storage standards. The high-value targets are mathematically shielded.
The only remaining targets are the “pirate treasures” of the early era—keys lost in landfills or on corrupted hard drives. If a quantum computer were to “steal” these coins, it would not be a theft of active user funds; it would be a form of involuntary asset recovery on coins the market has already priced in as “burned.”
Market Impact Analysis:
If these 10,000 “Zombie” BTC were to suddenly move, the market might experience a momentary flash crash driven by sentiment (“Satoshi is awake”). However, fundamentally, this event would not compromise the cryptographic integrity of the remaining 19 million Bitcoin protected by modern hashing. The risk is idiosyncratic, not systemic.
THE “DEATH WINDOW” STRESS TEST: VULNERABILITY IN MOTION
We have established that dormant Bitcoin (Cold Storage) in modern addresses functions as an impenetrable fortress. However, risk profiles change the moment the fortress gates open. The nightmare scenario for the maximalist is not when they sleep, but when they transact.
In institutional cybersecurity, two primary attack vectors dominate the bear thesis: the passive strategy of “Harvest Now, Decrypt Later” and the active strategy of “Real-time Interception.” We must dissect the technical feasibility of these scenarios using First Principles logic.
THE “HARVEST NOW, DECRYPT LATER” (HNDL) FALLACY
The HNDL strategy is the standard operating procedure for state-level intelligence. Agencies like the NSA or MSS intercept encrypted traffic today (diplomatic cables, bank wires, proprietary data), store it in massive server farms, and wait decades for quantum capabilities to break the encryption.
However, applying HNDL logic to the Bitcoin network constitutes a Category Error.
Why? Because HNDL applies strictly to encrypted data. As previously established, a Bitcoin Address (P2PKH) is the product of Hashing, not encryption. One cannot “decrypt” SHA-256—even with infinite computing power—because the original information was destroyed, not encoded.
- The Reality: An adversary can record your Bitcoin address in perpetuity, but they will never derive the Public Key simply by staring at the Hash.
- The Exception: HNDL is only a valid threat if the user practices Address Reuse. For modern institutional custody solutions that generate a fresh Change Address for every transaction, HNDL is a null threat.
THE MEMPOOL VECTOR: A 10-MINUTE ARBITRAGE
This is the only theoretically valid attack vector that warrants serious risk management. The vulnerability window opens precisely when the “Broadcast” button is pressed.
When a transaction is broadcast, the wallet transmits a data packet containing the digital signature and the Raw Public Key to the network. This packet enters the Mempool (Memory Pool)—the waiting room for unconfirmed transactions—before being selected by a miner for block inclusion (average time: 10 minutes).
During this 10-minute interval, the Public Key is mathematically “naked.”
The theoretical attack chain operates as follows:
- Interception: The attacker’s quantum sensors scan the Mempool in real-time. They detect a transaction moving 100 BTC and capture the revealed Public Key.
- Flash Calculation: The attacker executes Shor’s Algorithm to derive the Private Key from the Public Key.
- Front-Running: Upon deriving the Private Key, the attacker constructs a new transaction moving the 100 BTC to their own wallet.
- Fee Bribing: The attacker attaches a significantly higher transaction fee (gas fee) than the original owner.
- Execution: Rational miners select the attacker’s transaction (maximizing revenue). The attacker’s transaction is confirmed; the original is discarded.
The Engineering Gap:
For this arbitrage to succeed, the quantum computer must not only solve the encryption but must do so in under 10 minutes.
Breaking a key in ten years is one engineering challenge; breaking it in 600 seconds requires a computational leap of magnitude. We are discussing millions of Logical Qubits maintaining perfect coherence. The gap between “capability to break” and “capability to break instantly” is the difference between the Wright Brothers’ glider and a hypersonic jet.
GAME THEORY: THE SELF-DESTRUCT MECHANISM
Let us assume, for the sake of the stress test, that a hyper-fast quantum computer exists. Would it target the Bitcoin network? Here, Game Theory and economic incentives override physics.
Operating a quantum mainframe at the scale of millions of qubits requires cryogenic infrastructure and energy consumption rivaling a small city. The Burn Rate (OpEx) for this machine would be measured in millions of dollars per hour.
- Cost vs. Reward: Attacking a wallet containing 1 BTC ($100k) while burning $1M in operational costs is immediate bankruptcy.
- Target Selection: A rational economic agent would only target “Satoshi Era” wallets (likely lost keys) or massive institutional wallets (Exchanges/ETFs).
- The Valuation Paradox: Unlike physical gold, Bitcoin’s value is derived from the integrity of its ledger. The moment the first successful quantum hack on a major wallet occurs, the market confidence collapses. The price of Bitcoin would effectively trend toward zero.
- The Result: The attacker would successfully steal 10,000 BTC, only to find they are holding 10,000 worthless units of a failed protocol.
This is Mutually Assured Destruction. A rational actor possessing a quantum supercomputer has far higher ROI targets: breaking pharmaceutical trade secrets, sovereign military comms, or central bank gold reserve codes—assets that retain value even after being compromised.
THE GLASS HOUSE PARADOX: WHY TRADFI IS THE PRIMARY CASUALTY
The ultimate irony in institutional risk assessment occurs when a traditional banking executive questions Bitcoin’s quantum resistance while sitting atop a pile of digital dynamite with a lit fuse.
Want Sharper & Deeper Market Analysis?
Get exclusive insights that are logical, comprehensive, and unbiased. Start building your investment strategy based on data, not just assumptions.
The consensus narrative is inverted. Technical analysis indicates that the global banking rails (SWIFT, FedWire, Visa/Mastercard) possess a significantly higher Beta to quantum disruption than the Bitcoin network. The divergence stems from a fundamental architectural difference: Bitcoin is engineered for Privacy (obfuscating keys), whereas Banking is engineered for Identity (broadcasting keys).
EXPOSURE BY DESIGN: THE PKI VULNERABILITY
Modern banking infrastructure is built upon a trust protocol known as PKI (Public Key Infrastructure). Every time a user accesses a mobile banking portal or executes a wire transfer, a digital “Handshake” occurs.
In this process, the bank’s server is mandated to transmit a Digital Certificate (SSL/TLS) to prove its legitimacy and prevent phishing. The critical flaw? This certificate contains the bank’s Public Key.
- Banking Reality: The Public Key is exposed to the open internet 24/7/365. It is a static target. Any adversary can harvest this key and feed it into a quantum algorithm to derive the Private Key of the Certificate Authority.
- Bitcoin Reality: As established in the previous section, the Bitcoin Public Key (P2PKH) remains concealed behind a SHA-256 Hash firewall and is only revealed for the 10-minute duration of a transaction.
Traditional finance lives in a “Glass House.” They cannot hide behind Hashing because their protocol requires them to constantly shout “THIS IS ME!” to verify identity. To a quantum predator, a bank server is a stationary, illuminated target; a Bitcoin wallet is a dark, moving target.
THE COBOL INFERNO: FATAL TECHNICAL DEBT
The second systemic weakness is not purely cryptographic; it is logistical. It is the problem of Technical Debt.
The majority of Core Banking Systems still operate on COBOL, a programming language from the 1970s running on legacy IBM mainframes. This code is often described as “spaghetti code”—patched and layered over five decades, maintained by a shrinking workforce of retirees.
The transition to PQC (Post-Quantum Cryptography) represents a logistical nightmare for TradFi:
- Migration Scale: Banks must audit millions of lines of legacy code and replace standard RSA/ECC encryption with quantum-resistant algorithms (e.g., CRYSTALS-Kyber) without incurring a single second of downtime.
- Interoperability Deadlock: Bank A in New York cannot upgrade in isolation. It requires Bank B in London, Bank C in Tokyo, and the SWIFT messaging layer to upgrade simultaneously. Failure to synchronize results in a global liquidity freeze.
- Bitcoin Agility: Conversely, Bitcoin is modular, Open Source software. If the quantum threat materializes, Core Developers release a Soft Fork containing new signatures (e.g., Lamport Signatures). Nodes that wish to survive upgrade voluntarily. There are no board meetings; there is no inter-bank bureaucracy.
BLAST RADIUS: CENTRALIZATION IS THE WEAKNESS
The final differentiator is the Blast Radius of a breach.
Bitcoin is a decentralized system. If a quantum computer successfully cracks a single wallet’s Private Key, only the funds in that specific wallet are compromised. The remaining 19 million BTC remain secure. The damage is compartmentalized.
Banking is a centralized system. The security of millions of accounts often relies on a few Root CAs (Certificate Authorities).
- If a quantum actor cracks the Master Private Key of a major bank or Root CA, they can perfectly forge the institution’s identity.
- They could issue fraudulent transactions, drain corporate treasuries, or collapse trust in fiat currencies within hours.
In a State-Sponsored Cyberwarfare scenario, an adversary will not waste compute cycles targeting a retail Bitcoin wallet holding 0.5 BTC. They will target the heart of the clearing system to paralyze the enemy’s economy. In this scenario, Bitcoin functions not as the target, but as the Lifeboat while the banking carrier sinks.
THE GEOPOLITICAL GAME THEORY: WHY STATE ACTORS WON’T SHORT BITCOIN
In the geopolitical theater, technology is not merely a trade tool; it is a kinetic weapon. The prevailing retail panic—that a sovereign power (e.g., the U.S. or China) will deploy quantum capabilities to vaporize Bitcoin—portrays a naive understanding of statecraft and military doctrine.
If the NSA or the MSS achieves quantum supremacy tomorrow, the last action they will take is an attack on the Bitcoin network. We must dissect this rationale using military logic and strategic game theory.
THE “SILENT WEAPON” DOCTRINE: ASSET PRESERVATION STRATEGY
A stable, Fault-Tolerant Quantum Computer (FTQC) represents the apex of intelligence assets. Its strategic value parallels the breaking of the Enigma code in World War II.
If a nation-state possesses this capability, their operational priority is Total Stealth.
The primary targets are:
- Strategic Decryption: Intercepting nuclear launch protocols and submarine telemetry.
- Industrial Espionage: Exfiltrating semiconductor designs, pharmaceutical IP, or advanced battery chemistry.
- Grid Infiltration: The capacity to silently shut down an adversary’s power grid.
Attacking Bitcoin is a High-Noise Event.
The moment the first Bitcoin block is reorganized or a Satoshi-era wallet is drained, the global intelligence community will know that “Someone has broken secp256k1.” This triggers a global alarm. Adversaries will immediately rotate their nuclear codes and upgrade banking protocols.
Utilizing a quantum computer worth trillions to steal Bitcoin (which would crash to zero immediately following the hack) is strategic suicide. It is akin to using a tactical nuclear weapon to rob a convenience store; you acquire petty cash, but you reveal your ultimate weapon to the world.
THE FIAT DOOMSDAY SCENARIO: SYSTEMIC FRAGILITY VS. ANTIFRAGILITY
Let us simulate the worst-case scenario: A Quantum Attack occurs. How does the Fiat system respond compared to the Bitcoin protocol? This divergence defines the risk profile of your portfolio.
Scenario A: The Banking Breach (The Inflationary Bailout)
Imagine the SWIFT clearing system or the JPMorgan ledger is compromised. Customer balances are altered; trillions are deleted or siphoned.
- The Reaction: Central Banks have zero optionality but to execute a Bailout. Because fiat currency is a centralized database that can be edited, the Fed would “print” new liquidity to reimburse depositors to prevent social unrest.
- The Impact: Instant currency debasement. Trust in the currency collapses not due to technology, but due to the dilution of value. Your money is numerically safe, but its purchasing power evaporates.
Scenario B: The Bitcoin Breach (The Hard Fork Defense)
Imagine an attacker penetrates the digital signature scheme and begins liquidating coins.
- The Reaction: Bitcoin lacks a Central Bank to socialize losses. The solution is Social Consensus. The node operators and miners detect the anomaly immediately. Core Developers release an emergency Hard Fork to Rollback the chain to the block height prior to the attack, simultaneously implementing a new Quantum-Resistant signature scheme.
- The Impact: The network may experience downtime. Credibility takes a hit. However, the 21 Million Hard Cap remains inviolate. No new Bitcoin is printed to cover the loss.
THE ULTIMATE HEDGE: BITCOIN AS THE LAST LEDGER STANDING
Here lies the paradox: In a quantum cyberwar environment, the traditional banking system is fragile due to its reliance on centralized opacity and inflationary solutions.
Bitcoin, with its radical transparency, permits real-time auditing. If an attack occurs, it is visible instantly. If a Bank is hacked via a “salami slicing” attack (stealing fractions of cents over millions of transactions), the public remains oblivious until the annual audit—or until inflation explodes.
Therefore, the narrative that “Bitcoin dies in the Quantum Era” must be inverted. A post-upgrade (Quantum-Proof) Bitcoin may emerge as the sole immutable financial ledger left standing when global banking databases have been compromised and manipulated by state-level cyberwarfare.
CODE DARWINISM: THE POST-QUANTUM EVOLUTIONARY BLUEPRINT
The narrative that Bitcoin is a “static rock” incapable of adaptation is a fatal misunderstanding of open-source software dynamics. Bitcoin is not a pyramid waiting to erode; it is a digital biological organism that evolves based on environmental pressure.
If the quantum computer is the new apex predator, the Bitcoin codebase possesses the genetic mutation mechanism required to develop immunity. In this section, we dissect the “Plan B” of Bitcoin Core developers: How the network migrates from Elliptic Curve Cryptography (ECC) to Post-Quantum Cryptography (PQC) without arresting the global economic engine.
THE TAPROOT DILEMMA: REGRESSION OR OPTIMIZATION?
Before addressing the future, we must clarify the debate regarding the present. The Taproot upgrade (2021) introduced Schnorr Signatures. To the skeptical observer, this appeared to be a regression in quantum resistance.
The critique: Schnorr signatures possess a linear mathematical property that is, theoretically, slightly easier for Shor’s Algorithm to attack than standard ECDSA.
- Technical Reality: The differential in computational difficulty between breaking Schnorr vs. ECDSA is marginal. If a quantum machine can crack ECDSA with 4,000 Logical Qubits, it might crack Schnorr with 3,800.
- Strategic Analysis: In the scale of quantum engineering, this difference is a rounding error. There is no scenario where ECDSA remains secure while Schnorr collapses. They share the same risk profile. The privacy and scalability utility delivered by Schnorr vastly outweighs this marginal theoretical risk. Taproot is not a security flaw; it is an efficiency foundation.
THE DEFENSIVE ARSENAL: LAMPORT & LATTICE
If ECC collapses, what replaces it? The developer community does not need to invent new mathematics; they simply need to select from the existing menu of cryptographic defense. There are two primary candidates.
1. Lamport Signatures (The “Brute Force” Shield)
This is the emergency solution most likely to be adopted if a surprise attack occurs tomorrow.
- Mechanism: Lamport Signatures do not utilize complex elliptic curve math. They are based purely on Hash Functions. Since we have established that Hashes (SHA-256) are quantum-resistant, these signatures inherit that immunity automatically.
- The Trade-off: Data weight. A single Lamport signature can consume several kilobytes (compared to Schnorr’s 64 bytes).
- Impact: Adoption would cause blockchain bloat and transaction fees would spike violently. However, as a “panic button” to preserve global wealth, this is an acceptable cost of capital.
2. Lattice-Based Cryptography (The “Elegant” Shield)
This is the long-term solution currently being standardized by NIST (National Institute of Standards and Technology).
- Mechanism: Utilizes multi-dimensional mathematical problems (finding the closest vector in a 1,000-dimension grid) that render even quantum computers impotent.
- Advantage: Signature sizes are significantly smaller than Lamport, preserving network efficiency. Algorithms such as Dilithium or FALCON are strong candidates for inclusion in future Soft Forks.
THE UPGRADE MECHANISM: OPEN-HEART SURGERY AT SPEED
How do we replace the cryptographic foundation of a vehicle moving at 200 mph? The answer is the Soft Fork.
We do not require a contentious “Hard Fork” that fractures the community (reminiscent of the Bitcoin Cash wars). Bitcoin possesses flexibility through new address types (e.g., SegWit introduced ‘bc1’).
- Phase 1: Protocol Implementation (P2PQC)
Developers release a Soft Fork introducing a new “Pay-to-Post-Quantum” (P2PQC) address standard. These addresses utilize Lamport or Lattice signatures. - Phase 2: Voluntary Migration
The network does not force migration. However, major custodians (Coinbase, Fidelity) and institutional allocators will begin moving Cold Storage to P2PQC addresses for long-term insurance. - Phase 3: Natural Selection
Legacy addresses (P2PKH) remain functional, but the market will likely assign a “risk discount” or higher insurance premiums to them. Liquidity will organically flow toward the quantum-proof standard.
Bitcoin does not need to “defeat” the quantum computer today. It simply requires a clear evacuation route. That route already exists in the mathematical blueprints, waiting for consensus to activate.
THE MIGRATION EVENT: A MANUAL FOR DIGITAL EVACUATION
We frequently discuss network upgrades in the abstract, yet analysis rarely accounts for the execution friction imposed on the end-user. If and when the Post-Quantum Cryptography (PQC) Soft Fork is activated, Bitcoin will not magically secure itself within your custody solution. Action is required.
This is not a passive iOS update that occurs while you sleep; it is a migration of digital bearer assets. We must simulate “Transition Day” to prevent decision paralysis during a high-volatility event.
THE EXODUS PROTOCOL: EXECUTION MECHANICS
Upon activation of the P2PQC (Pay-to-Post-Quantum) protocol, the Bitcoin network effectively bifurcates into two security zones: The Red Zone (Legacy, SegWit, Taproot addresses) and the Green Zone (New PQC addresses).
Your mandate as an allocator is to migrate AUM from the Red Zone to the Green Zone.
- Fortress Construction: You must generate a new Seed Phrase or deploy a new custody vault that supports the PQC cryptographic standard (e.g., Lattice signatures).
- The Evacuation Transaction: You must execute an on-chain transaction, sweeping assets from the legacy address to the new address.
Here lies the operational bottleneck: The Quantum Congestion.
Visualize millions of users—from retail wallets to Tesla’s corporate treasury—attempting to rotate keys simultaneously. The transaction queue (Mempool) will succumb to unprecedented pressure. Transaction fees (gas fees) will decouple from their historical averages; we are not discussing cents, but potentially hundreds of dollars per transaction.
This is the Quantum Tax.
Early movers who migrate during the “Phase 2 Voluntary” window will pay standard rates. Those who wait for a CNN headline declaring a quantum emergency will pay a massive premium to compete for scarce blockspace.
THE CANARY IN THE COAL MINE: ON-CHAIN LEADING INDICATORS
When should the migration begin? Waiting for an official press release from Google or a state government is a losing strategy; public information is always lagging. As forensic analysts, we must monitor On-Chain Leading Indicators.
Recall the 10,230 “Zombie Coins” (P2PK) discussed in Part 3. These serve as our “Canary in the Coal Mine.”
- Baseline Scenario: These archaic UTXOs remain dormant.
- The Q-Day Signal: If these Satoshi-era P2PK addresses mobilize without a valid digital signature or exhibit mathematically anomalous transaction patterns, this is the Red Alert.
Why these specific coins? Because P2PK addresses are the lowest-hanging fruit. If a quantum entity becomes operational, they will harvest these exposed assets first as a “Proof of Concept” before attacking harder targets (P2PKH).
If Whale Alert signals movement from these wallets, and the cryptographic community flags the signatures as irregular, it is the starting gun. You must begin the asset migration immediately, regardless of the fee environment.
SIGNAL VS. NOISE: AVOIDING THE FALSE FLAG
However, the sophisticated investor must guard against manipulation. The movement of legacy coins could simply be an early miner recovering an old hard drive. Do not succumb to blind panic.
The differentiation lies in the Verification Math:
- Scenario A: The coins move with a valid ECDSA signature. This is a legacy owner cashing out. Assessment: Safe.
- Scenario B: The coins move, but network validators reject the block, or we observe a suspicious chain reorg. This indicates a quantum entity is attempting to forge signatures. Assessment: Attack Imminent.
Preparation for this event is not about fear; it is about technical literacy. You must possess the capability to interpret a block explorer, rather than relying on mainstream financial news headlines.
THE ANTIFRAGILE VERDICT: ENGINEERING RESILIENCE AT THE QUANTUM EDGE
We have dissected the anatomy of this fear from the sub-atomic level to the geopolitical stage. We have established that the “Quantum Apocalypse” is not an inevitable typhoon, but a quantifiable engineering challenge. Now, we must execute the strategic conclusion: How does one position capital based on this intelligence?
To answer, we must view the board through the lens of the dominant market participants who possess information asymmetry far superior to the average retail speculator.
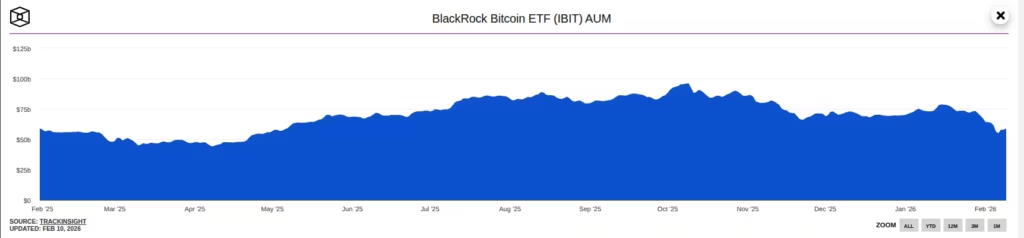
THE SILENCE OF THE WHALES: WHY SMART MONEY IS LONG
The loudest signal in the market is not a CNN headline; it is institutional Money Flow.
Consider the due diligence capability of the incumbents: BlackRock, Fidelity, and Vanguard employ armies of PhDs in physics, mathematics, and risk management. They possess direct channels to the quantum research divisions of IBM and Google. If the quantum threat were existential and unsolvable within a 10-year horizon, would they risk their reputation and billions in client capital to launch Spot Bitcoin ETFs?
The answer is No.
The aggressive institutional accumulation of Bitcoin in the current environment is the highest form of Alpha.
- Institutional View: They categorize quantum risk as the crypto equivalent of the “Y2K Problem”—a technical bug requiring a capital-intensive patch, not an asteroid event that extinguishes the asset class. They understand the protocol is upgradeable.
- Strategic Hedging: Paradoxically, they view Bitcoin as a hedge against the fiat banking system which, as discussed in Part 5, is structurally more vulnerable to cyberwarfare due to its COBOL legacy.
THE LIQUIDITY TRAP: FUD AS A MECHANISM FOR WEALTH TRANSFER
On the opposite end of the spectrum lies Retail Behavior. Whenever a mainstream article regarding “Google’s Quantum Breakthrough” circulates, retail forums capitulate. “Sell now before it goes to zero” becomes the consensus mantra.
This represents a classic market dynamic: The transfer of wealth from the impatient (and uneducated) to the patient (and informed).
The “Quantum Apocalypse” narrative is frequently recycled by mainstream media during critical market inflections to generate sell-side liquidity. The sophisticated investor must interpret this FUD (Fear, Uncertainty, Doubt) as a discount mechanism. If you liquidate Bitcoin due to fear of a non-existent computer, you are effectively donating scarce assets to institutions that have already priced in the migration solution.
THE REAL THREAT MATRIX: GOVERNANCE RISK VS. MATHEMATICAL RISK
As honest analysts, we must not adopt a blind perma-bull stance. Risk exists. When should the panic button actually be pressed? Not when Google releases a press release, but when Social Consensus Fails.
The only vector capable of killing Bitcoin is not the mathematics of Shor’s Algorithm, but Governance Failure.
- The Gridlock Scenario: If the Post-Quantum Cryptography (PQC) solution is code-ready, but miners, developers, and node operators fail to agree on implementation due to internal politics or ego.
- The Civil War Scenario: If a schism erupts regarding which encryption standard to adopt (Lattice vs. Lamport), resulting in a prolonged Chain Split.
As long as the community unites to execute the Soft Fork, the mathematics favor Bitcoin. If the community fractures, that is the signal to “Short” the market.
CLOSING THESIS: THE DEFINITION OF ANTIFRAGILITY
Nassim Taleb introduced the concept of Antifragility: A system that strengthens when subjected to stress, shock, or volatility. Human bone densifies under load; the immune system learns when exposed to pathogens.
Bitcoin is the textbook definition of Antifragility.
- It was attacked by regulators; it became more decentralized.
- It was attacked by the China Mining Ban; hashrate distributed globally.
- Now, it is threatened by quantum physics.
The outcome? This threat will force Bitcoin to evolve into Quantum-Proof Bitcoin. The version of the protocol that survives the PQC upgrade will emerge as the hardest form of money ever engineered by humanity—immune to central bank inflation, state censorship, and even quantum mechanics.
The quantum threat is not the end of Bitcoin. It is the necessary catalyst to propel the asset to its next evolutionary stage. The question is not whether Bitcoin will survive, but whether you possess the High Conviction to hold the asset through its metamorphosis.
Disclaimer: The content provided by corequil.com is for information and education purposes only and is not intended as investment or financial advice. Please do your own research (DYOR) as your actions are your own responsibility. Check the Terms and Conditions for more information.